services
Computer Forensics

Computer forensics includes data analysis and recovery services that are used in a vast range of situations. Retrieving information from devices in a structured way is key to ensuring information is not lost. Deleted files, hidden files, and other useful content can be retrieved from computers, phones, storage media, and storage devices. Whether used in investigations, monitoring, or retrieval of important documents, forensics techniques are a powerful tool for several sectors and or industries.
Automation

Nothing highlights unification more than bringing it to the ease of your palm. We’ve expanded on this concept to bring you a unified and functional system for your home, office or even a building. Automation provides our customers with the ability to manage devices throughout their premises from wherever they want, whether it is locally from their TV set or remotely over the internet. Manage surveillance systems, control audio/video, set and manage timers for various tasks, manage household lighting, and so much more. Our services in this area makes the client safer, at ease and in control.
Identity Management

Our portfolio includes implementing systems for Identity management, or in better terms, the ability to manage individuals in terms of their system usage, information access levels, and credential verifications. It comes down to authorization and authentication, two similar looking terms with very different meanings. We help you control who has access to what resources, and also ensure that a person is who they claim to be. These systems come into play whenever identification of individuals is needed or whenever information needs to be restricted to a set individual or groups of individuals.
Information Systems Security Consulting

It is often difficult to know what security an organization requires and the benefits associated with employing different information security technologies. We offer guidance in this area. Taking an in-depth look at an organization’s needs, budget, and risks, we provide specially tailored security portfolios that meet the needs of our customers.
IS Vulnerability & Penetration Testing

Each day, vulnerabilities are found in software, policies, and procedures. Whether they exist on an in-house system or an outsourced system, having unauthorized persons penetrating into your infrastructure can be devastating. Even the harmless snooper can cause grave financial loss to an organization. Our services offer the ability to test your systems and determine if they successfully stand up to an attacker’s attempts to gain unauthorized access. We further look at mitigating the impact on situations that cannot be eliminated, such as penetration due to human error or deception by an attacker. With this, we also help identify attack attempts and breaches in the event that something has gone wrong and the organization can then move into a disaster recovery mode.
Law Enforcement ISS

In our growing economies, technology is a major player to provide quick action, quick results, and flexibility. Many devices, services, and software can be built or leveraged to enhance the effectiveness of key tasks. We specialize, but are not limited to, enhancing the systems of law enforcement through the use of customized software, RFID tagging devices, and working with existing procedures to maximize effectiveness and ensure compatibility with current policies. We look at current and future requirements, propose a plan for enhancement, and complete the plan from the ground up to provide the most tailored and effective solutions.
Network Management

Our network management services ensure that the Client network retains or exceeds all the aspects expected. Our focus is to ensure network availability, efficiency, and security. From device optimization, to access restricting, to log management, to device upgrading, and many more services. We ensure that your key infrastructure works at its best. Whether they need an expert team to manage their existing infrastructure, to fix problems created by others in the networking industry, or to design and manage their network from birth, we provide our services in every aspect of their networking needs.
Remote IT

Computer problems are all too well known in business. Management of systems is a necessity. We understand the requirements for making changes and fixing problems quickly and effectively. Our company offers remote Information Technology services. This means that our knowledgeable staff can quickly respond to customer needs and concerns without the lost time that comes from traveling. Many computer related problems can be solved remotely, and those that can’t are identified remotely and acted upon in a timely manner. Remote Information Technology brings an efficient and systematic approach to IT management that saves you time and money.
RFID Solutions
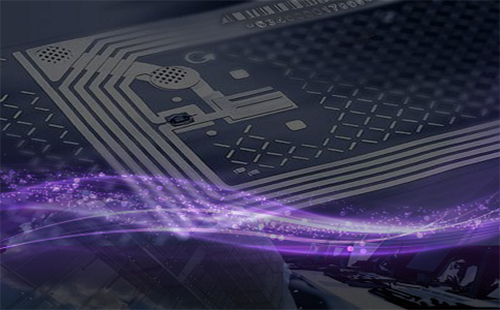
With technology at the forefront of innovation, RFID devices play a major role towards increasing efficiency and reliability in a wide range of situations. Our company leverages this technology to provide custom solutions for our customers. How this benefits you depends greatly on your current procedures and plans for expanding. RFID technology is small yet very powerful. If you are looking to increase your organization’s efficiency, add new and improved methods for accomplishing manual tasks, or want an effective method of identification, control, or monitoring, then our offerings in this area can build a custom solution for you. Our team of experts are glad to discuss with you the benefits of utilizing this technology within your organization.
Risk Assessment

As an organization, it is very important to be proactive and prepare for any threats to the business. To do this, there must be an understanding of the risks involved, from natural disasters to rogue employees. We provide a comprehensive look at the risks that business faces; the financial cost of protecting against them and the potential damages to the company, financial and otherwise, caused from ignoring the threat.
Risk Management

Once you know what you are at risk for, you must consider what measures to take that will insure the best business continuity with the lowest down time and lowest financial loss. Our risk management services help the client with this very thing. We evaluate the risks to their company and look in detail at the cost benefit analysis of implementing protection measures versus accepting the damages as they occur. By focused analysis of each risk, companies are better positioned financially and otherwise through implementation of key initiatives.
Secure Software Developing

When developing unique projects, the demand for unique solutions needs to be implemented. In these cases, we develop software programs that meet your needs. In doing these development projects, security features are best implemented from the start to avoid future concerns. We bundle all this into one comprehensive package that is custom tailored and as strict or flexible as is required. Anything from large scale software that is used by large groups or ones designed for small teams.
Secure Unified Communication

Our company is all about security. This means we strive to protect our customers, their privacy, and the confidentiality of the information they read and/or send out. Unified communication is the technology where one person, a group of people, or a corporation, can synchronize all their information and share it in amazing ways to accomplish astounding results. In this service, we combine the best of both worlds, providing the power of data sharing across devices and locations, while ensuring the information transmitted is safe, reliable, and not readable by prying eyes. These components on their own are not nearly as powerful as they are when combined. Our experts have been trained to come up with custom tailored solutions for individuals, businesses, and corporations that incorporate these key aspects to produce what we call “Secured Unified Communication”, providing freedom, functionality, and peace of mind.